Campus Wi-Fi is a convenient resource for students and staff alike, but it’s important to understand the extent to which your activity on these networks can be monitored and tracked.
Many schools implement network policies and restrictions to maintain security and enforce acceptable use.
However, these policies often raise questions about privacy and the technical capabilities of campus IT departments. Let’s dive into the details of how campus networks operate, the role of VPNs, and what you can do to protect your privacy.
Can Schools Track Your Internet Usage?
Yes, schools can track your internet usage on their Wi-Fi networks.
Here are the primary ways they do it:
- IP and MAC Address Tracking: When you connect to a Wi-Fi network, your device is assigned an IP address, and your network interface card (NIC) broadcasts a MAC address. These identifiers help the network manage connections and allow administrators to track which devices are accessing their infrastructure.
- Device Identification: Many devices broadcast their names—such as “John’s iPhone” or “Jane’s Laptop”—when connecting to a network. This can make it easy for IT staff to identify specific users, especially if your device name includes your real name.
- Access Point Logs: Schools often use multiple access points (APs) throughout their campus. These APs can log when and where a device connects, allowing administrators to track movement across the campus. If your device frequently connects to an AP in a specific dorm or classroom, it can narrow down your identity.
- Login Credentials: If your school requires you to log in with a student ID and password to access Wi-Fi, this ties your activity directly to your identity. Network Access Control (NAC) systems can send user information to firewalls, enabling detailed monitoring and enforcement.
Can Schools Legally Monitor Certain Activities?
The legality of monitoring student activities on campus networks involves a complex interplay between privacy rights, institutional policies, and the ownership of the network infrastructure. Educational institutions are generally within their rights to monitor activity on their networks, but this authority is not without limits, particularly when it comes to respecting individual privacy.
Boundaries of Acceptable Monitoring
Schools typically justify monitoring on-campus network activity by citing the need to maintain security, enforce acceptable use policies, and ensure compliance with legal requirements such as the Children’s Internet Protection Act (CIPA) for K–12 institutions. However, this justification must align with legal and ethical standards:
Transparency and Consent
- Institutions are required to inform students and staff about monitoring practices through acceptable use policies (AUPs) or similar agreements. These documents should outline the extent of monitoring, the types of data collected, and the purpose of such activities.
- By connecting to the campus network, users often implicitly consent to these terms. However, ambiguity in the AUP or failure to communicate the policy clearly could lead to legal challenges.
Scope of Monitoring
- Schools can monitor network traffic, including websites visited, applications used, and data transfer volumes. However, they generally cannot intercept the content of encrypted communications (e.g., HTTPS traffic or messages on encrypted platforms) unless users have installed a school-provided certificate allowing such access.
- Monitoring should focus on legitimate concerns, such as detecting unauthorized access, preventing cyber threats, or identifying violations of institutional policies. Excessive or overly invasive monitoring, particularly without proper disclosure, may be deemed an infringement on privacy rights.
Legal Protections
- In many jurisdictions, students and staff retain a reasonable expectation of privacy for personal communications, even on school-provided networks. For example, intercepting the content of private messages without consent could violate laws such as the Electronic Communications Privacy Act (ECPA) in the United States.
What About VPNs? Are They Foolproof?
Virtual Private Networks (VPNs) are often touted as the go-to solution for online privacy.
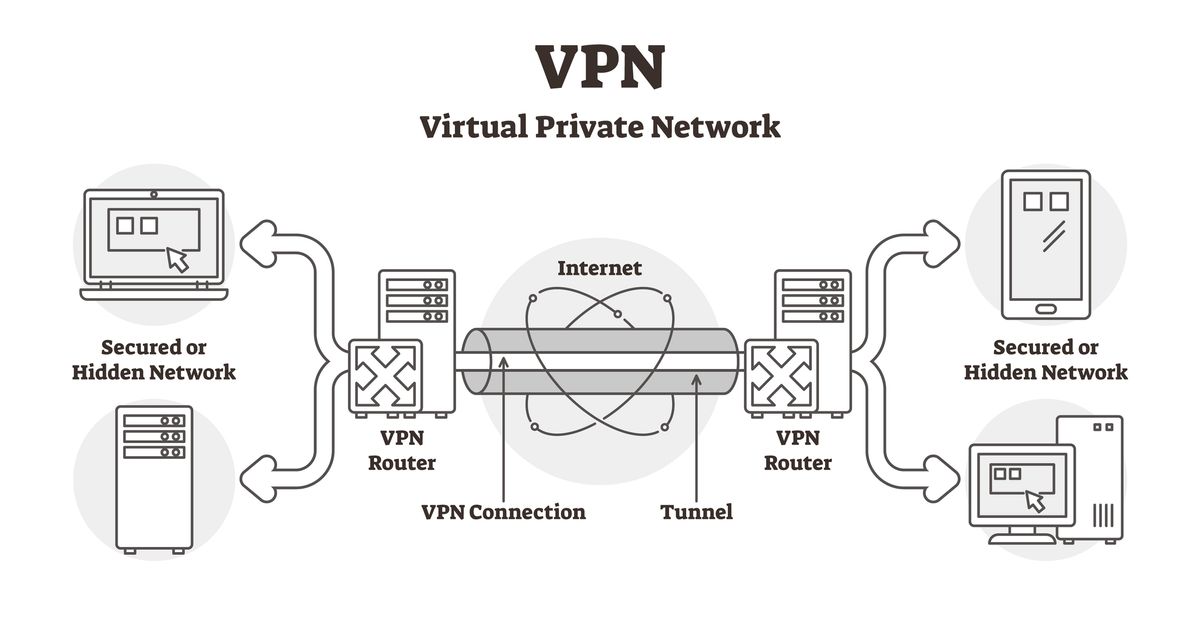
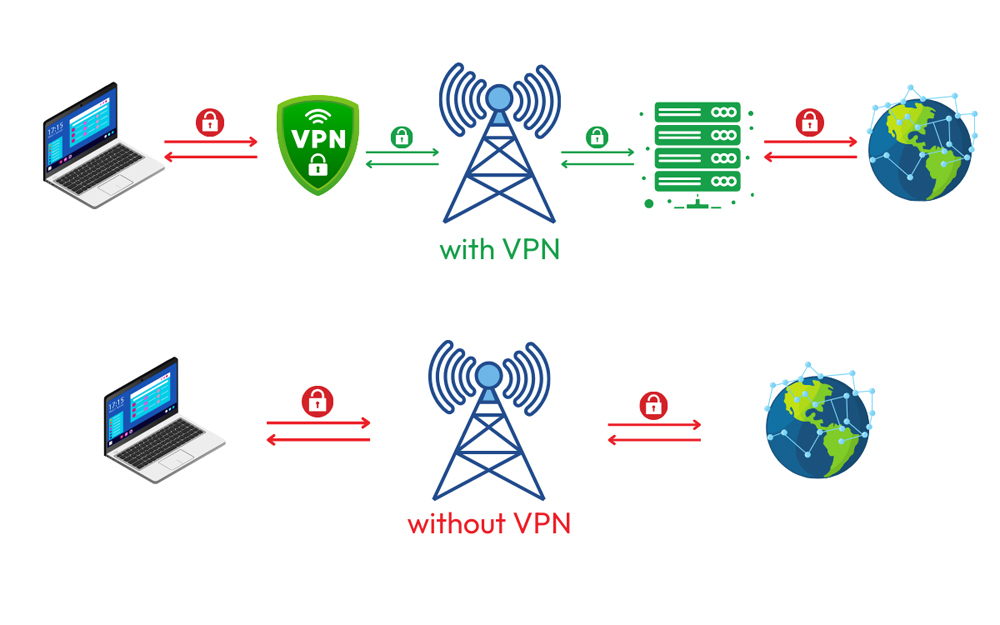
While they do provide a layer of encryption, VPNs aren’t completely foolproof on campus networks. Here’s what you should know:
- VPN Detection: Schools can detect VPN traffic by identifying the specific ports and IP addresses commonly used by VPN providers. They might block these connections altogether, making it difficult for you to establish a VPN tunnel.
- Traffic Visibility: A properly configured VPN encrypts all your data, making it unreadable to anyone monitoring the network. However, if the VPN isn’t set up correctly, DNS queries or other data may leak outside the encrypted tunnel, exposing some of your activity.
- Misconceptions About VPN Decryption: Claims that schools can “outsmart” or decrypt VPN encryption are typically exaggerated. Breaking modern encryption would require advanced resources, such as those available to national security agencies, which is beyond the reach of most educational institutions.
- Policy Enforcement: Even if schools can’t see what you’re doing on a VPN, they can still penalize you for using one if their network policies prohibit it. Simply detecting VPN traffic might be enough to raise red flags.
Advanced Monitoring Tools Used by Schools
Some schools employ sophisticated technologies to manage and monitor their networks. These include:
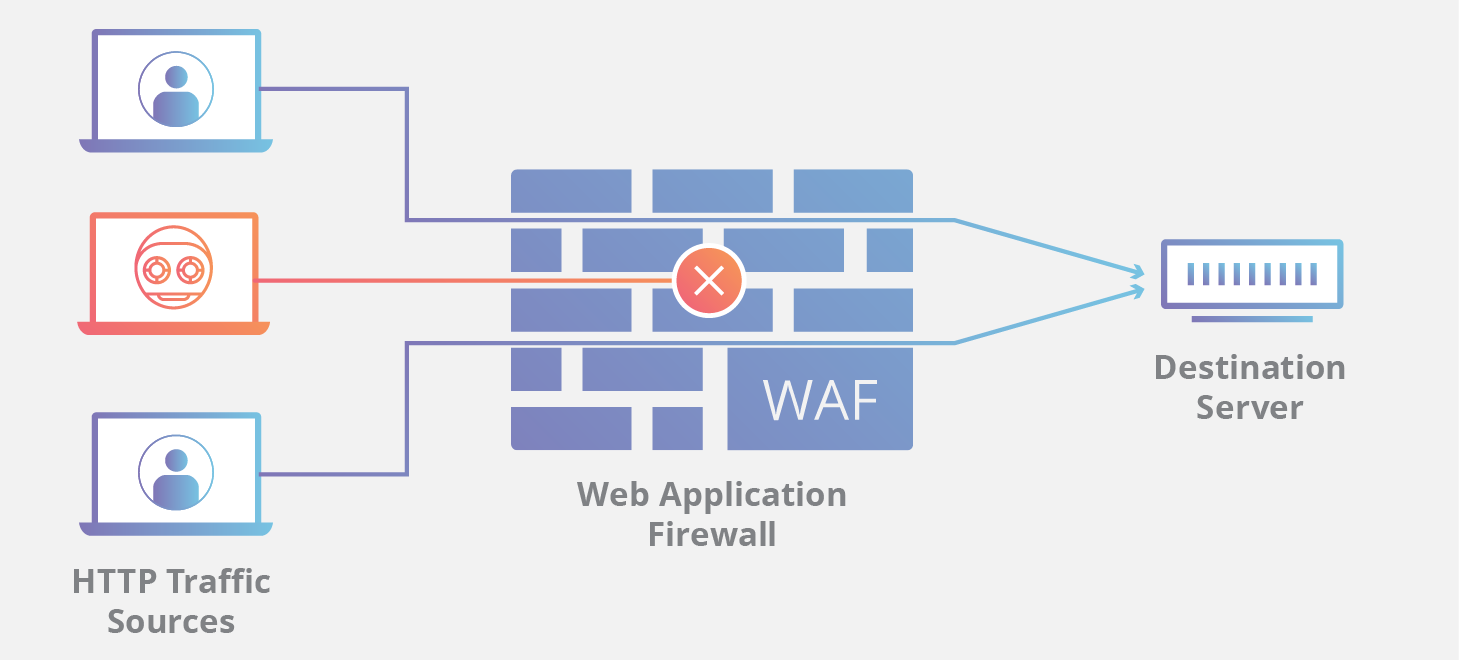
- Transparent Proxies: These devices sit between the user and the internet, intercepting and analyzing traffic. While they can’t decrypt VPN traffic, they can flag VPN usage itself.
- Application-Aware Firewalls: Tools like Cisco ISE and Palo Alto firewalls can block specific applications, including common VPN software, and even identify the type of device or operating system being used.
- Geolocation Tracking: By mapping access points, IT departments can track a device’s physical location within the campus, sometimes with surprising accuracy.
Privacy Concerns and Practical Realities
While schools often emphasize their ability to monitor and control network activity, the reality is usually less invasive than it sounds.
Many IT departments have limited budgets and staff, making it unlikely they’ll spend extensive resources tracking individual students. However, you should still assume that basic monitoring is in place and act accordingly.
Tips for Protecting Your Privacy on Campus Wi-Fi
If you value your privacy while using campus Wi-Fi, here are some steps you can take:
- Use a VPN: A reputable VPN service can encrypt your data, making it unreadable to anyone monitoring the network. Be sure to configure it properly to avoid DNS leaks.
- Rename Your Device: Avoid using your real name or any identifying information in your device’s name. For example, change “John’s iPhone” to something generic like “Device123.”
- Enable Private MAC Addresses: Many modern devices allow you to randomize your MAC address. This makes it harder for networks to track your device across sessions.
- Stick to Cellular Data: For sensitive or private activities, consider using your mobile data instead of campus Wi-Fi. This bypasses the school’s network entirely.
- Understand Network Policies: Familiarize yourself with your school’s acceptable use policy. Knowing what’s allowed can help you avoid unintentional violations.
Is It Ever Possible to Be Truly Anonymous on Campus Wi-Fi?
Achieving complete anonymity on campus Wi-Fi is an ambitious goal, but it is technically possible to enhance privacy by employing a combination of tools and techniques, such as a VPN, the Tor browser, private DNS, and randomized MAC addresses. However, even with these measures, there are practical limitations that make total anonymity difficult to achieve. Let’s examine each component in detail and discuss the constraints of this approach.

Combining Tools for Anonymity
- VPN (Virtual Private Network):
- A VPN encrypts your internet traffic and routes it through an intermediary server, masking your IP address and hiding your online activities from the network provider.
- Effectiveness: While a properly configured VPN can shield your traffic from network administrators, it does not make you entirely anonymous. The VPN provider itself can potentially log and identify your activity unless a strict no-logs policy is in place.
- Risks: Some campus networks actively detect and block VPN traffic, raising red flags or denying access to specific services.
- Tor Browser:
- The Tor browser enhances anonymity by routing your internet traffic through a network of volunteer-operated servers, concealing your IP address and encrypting your communications at multiple layers.
- Effectiveness: Tor offers strong anonymity, particularly for accessing websites and services that support Tor’s protocol. However, its performance may be slow, and not all services or websites are accessible through Tor.
- Risks: Simply using Tor can attract attention, as its traffic patterns are easily identifiable, even if the content remains encrypted. This can lead to scrutiny from network administrators.
- Private DNS:
- Configuring your device to use a private DNS service (e.g., Cloudflare DNS or Google DNS) ensures that your DNS queries are encrypted and not visible to the campus network.
- Effectiveness: This prevents the network from logging which websites you attempt to visit. However, it does not obscure the destination IP addresses of your traffic.
- Risks: If your VPN or Tor browser is not configured to route all DNS requests through their network, DNS leaks could expose your browsing activity.
- Randomized MAC Addresses:
- Modern devices often allow users to enable MAC address randomization, which generates a unique, temporary MAC address for each network session. This makes it harder for administrators to track a specific device across multiple connections.
- Effectiveness: This measure can effectively disrupt tracking based on device identifiers, especially when combined with other privacy tools.
- Risks: MAC randomization is not foolproof. Some networks disable access for devices with randomized MAC addresses or can still identify patterns through other metadata, such as connection times or traffic behavior.
Practical Limitations of Anonymity Measures

- Correlation of Metadata: Even with encryption and randomized identifiers, network administrators can analyze metadata—such as the timing, volume, and destination of your traffic—to infer patterns. For instance, consistently accessing specific services (e.g., video streaming) or connecting at the same time each day can create a recognizable profile.
- Device Fingerprinting: Advanced monitoring tools can identify unique characteristics of your device, such as its operating system, browser configuration, or software versions. This device fingerprinting can persist even if other identifiers, like IP or MAC addresses, are hidden.
- Behavioral Patterns: Your online behavior, such as the websites you visit or the services you use, can reveal your identity over time. For example, frequenting a specific social media platform or accessing personal accounts may compromise anonymity.
- Network Policies and Restrictions: Some institutions actively block or restrict privacy tools such as VPNs, Tor, or private DNS. Attempting to circumvent these restrictions may draw attention and could lead to consequences under the school’s acceptable use policy (AUP).
- Human Error: The complexity of managing multiple tools simultaneously increases the risk of misconfiguration. A single oversight, such as failing to route all traffic through a VPN or leaking DNS queries, can compromise anonymity and expose your activity.
- Legal and Ethical Considerations: While technical measures can enhance privacy, users must be aware of the legal and ethical implications of attempting to bypass campus monitoring systems. Violating network policies, even for legitimate privacy concerns, can result in disciplinary action or loss of access to campus resources.
Key Takeaways
Using campus Wi-Fi comes with trade-offs. While it’s convenient and free, it’s also a controlled environment where your activity can be monitored. By understanding how these networks work and taking basic precautions, you can better protect your privacy and ensure a smoother online experience. Remember, when you’re on someone else’s network, they set the rules—so it’s always wise to browse responsibly.
